You have sites, vehicles, IoT, and remote workers — all requiring reliable, secure, and agile connectivity. Cradlepoint 5G and LTE Wireless WAN, private cellular network, and cybersecurity solutions enable the freedom to securely connect more experiences, new ways to work, and improved business results.
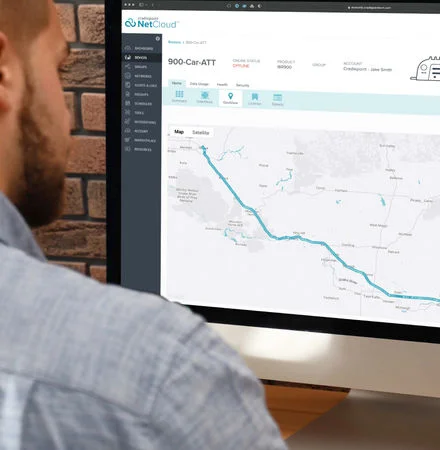
Embrace Wireless WAN and private network solutions with unmatched agility and reach through Cradlepoint NetCloud.
Secure and reliable
Have the peace of mind that comes from reliable, high-performance connectivity through wireless solutions with integrated security. Thousands of enterprises count on cloud-managed routers and adapters for WWAN and private cellular networks every day.
Versatile and scalable
With the broadest range of use cases and solutions, Cradlepoint offers the flexibility to embrace new ways of doing business anywhere, and to always put your best network forward. We provide scalability suited to fast-moving business transformation.
Simple and sophisticated
Cellular broadband goes up immediately and with ease — especially with zero-touch deployment through Cradlepoint’s plug-and-play solutions. And with Cradlepoint NetCloud, real-time network visibility and control are at your fingertips.
Unlock the power of LTE and 5G with Cradlepoint Cellular Intelligence in more places and ways — without conventional limitations.
Sites
Welcome the freedom of LTE and 5G solutions for hybrid WAN and failover in fixed, temporary, and pop-up locations — enabling any combination of Wired and Wireless WAN.
Learn moreVehicles
Optimize mobile broadband and Wi-Fi across connected vehicle fleets of any size, enabling 24×7 access no matter the route.
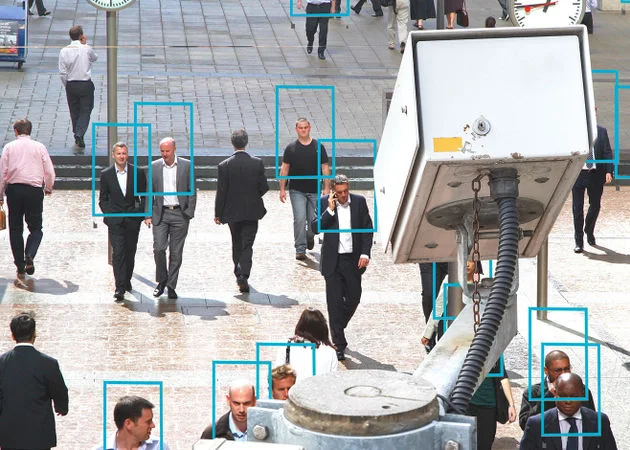
Learn moreIoT
Use reliable, agile cellular IoT connectivity to harness the vast potential of edge data with undelayed deployments and unfettered innovation.
Learn moreRemote Work
Equip remote employees with reliable dedicated connections through SOHO routers that the IT team can control from anywhere.
Learn more